Windows Defender is anti-spyware software that's included with Windows 10 and runs automatically when it's turned on is just as important as the SmartScreen in Win-10 .Content / Solution / Tip: 1.) ... The Defender Protect the Windows!
|
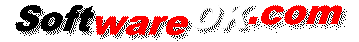
| (Image-1) Defender W10! |
 |
See also:
► ... help, Windows 10 Defender is turned off or Permanently Disable? (on, Enable)
► ... The virus scanner never finds anything, do I need something like this under Windows-10?
When you use Windows Defender, it's important to have up-to-date definitions. Definitions are files that act like an ever-growing encyclopedia of potential software threats. Windows Defender uses definitions to alert you to potential risks if it determines that software detected is spyware or other potentially unwanted software. To help keep your definitions up to date, Windows Defender works with Windows Update to automatically install new definitions as they're released. You can also set Windows Defender to check online for updated definitions before scanning. For information about keeping your definitions up to date and how to manually download the latest definitions, see Keep Windows Defender definitions up to date.
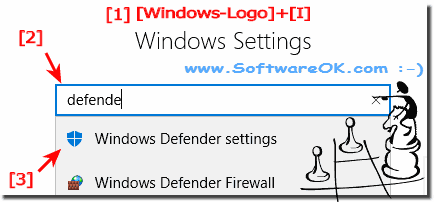
| (Image-2) Prevent viruses spyware on Windows 10? |
 |
Useful info from (c) Microsoft:
A virus is a program that replicates itself. It spreads by making copies of itself on a computer or by inserting computer code into program or operating system files. Viruses don't always damage files or computers, but they usually affect a computer's performance and stability. For a virus to infect a computer or to spread, you usually have to do something, such as open an infected e‑mail attachment.
A worm is computer code that spreads without user interaction. Most worms begin as e‑mail attachments that infect a computer when they're opened. The worm scans the infected computer for files, such as address books, or temporary webpages, that contain e‑mail addresses. The worm uses the addresses to send infected e‑mail, and often mimics (or spoofs) the "From" addresses in subsequent e‑mail messages so that those infected messages appear to be from someone you know. Worms then spread automatically through e‑mail, networks, or operating system vulnerabilities, often overwhelming those systems before the cause is known. Worms aren't always destructive to computers, but they usually cause computer and network performance and stability problems.
A Trojan horse is a malicious software program that hides inside other programs. It enters a computer hidden inside a legitimate program, such as a screen saver. It then puts code into the operating system, which enables a hacker to access the infected computer. Trojan horses do not usually spread by themselves; they are spread by viruses, worms, or downloaded software.
Protect you Win10 PC!
2.) Detected Top 10 Malware example!
malware (ai score=100)
Win32:Malware-gen
.UnclassifiedMalware
Malware:Variant.Mal.FA433741
VB:Malware.Malyria.12454
Malicious.Code.Virus.Troj.77
VB:Malicious.Virus.Troj (score=100))
malware (ai score=96)
Agresiv malware (ai score=100)
Malware_GEN.1300710RT
Info:
This screenshots has been snipped ergo created under Windows 10 Desktop PC Home Ver., However, you can use this example, as a prevent viruses on Windows solution without hesitation also use for earlier Microsoft's Windows 10 Builds whatever it's a Windows desktop, tablet, Surface Pro / Go, or even a server operating system. It has been tested on all and successfully verified.
This screenshots has been snipped ergo created under Windows 10 Desktop PC Home Ver., However, you can use this example, as a prevent viruses on Windows solution without hesitation also use for earlier Microsoft's Windows 10 Builds whatever it's a Windows desktop, tablet, Surface Pro / Go, or even a server operating system. It has been tested on all and successfully verified.
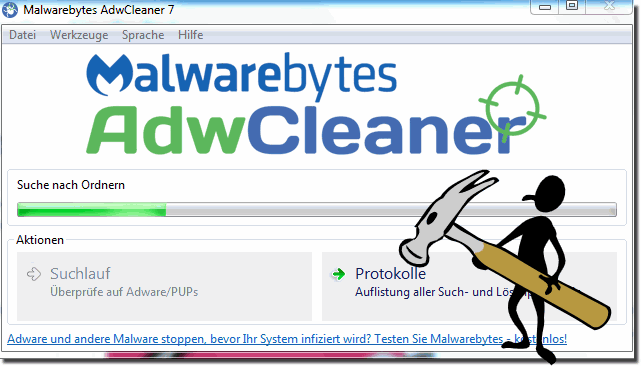
3.) Against adware, junkware, malware, MultiPlugs, toolbars or hijackers!
►►► .... www.softpedia.com/get/Antivirus/Removal-Tools/AdwCleaner.shtml| (Image-2) Arware, junk, spy Windows 10! |
 |
4.) 4.) ... Is Windows Defender good enough?
When you install Windows 10, an anti-virus program called Windows Defender is already running. Built into Windows 10, it automatically scans programs you open, downloads new definitions from Windows Update, and provides a user interface that you can use for incoming scans. The best thing about it is that it almost does not slow down your system, and it mostly does.
In short, yes: Windows Defender is good enough as long as you pair it with a good anti-malware program, as mentioned above.
FAQ 124: Updated on: 25 August 2023 12:30